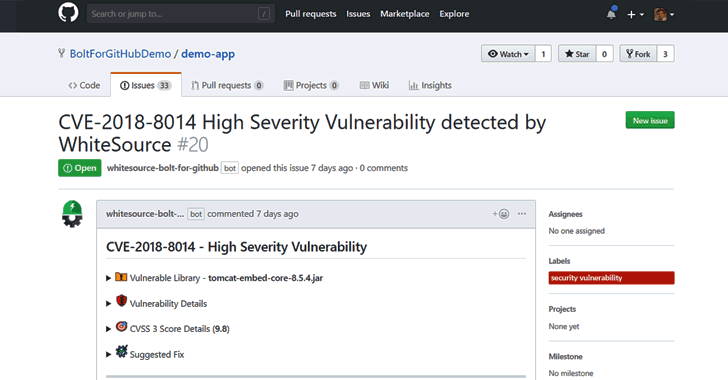
WhiteSource Bolt for GitHub: Free Open Source Vulnerability Management App for Developers
Developers around the world depend on open source components to build their software products. According to industry estimates, open source components account for 60-80% of the code base in modern applications.
17
